short introduction
when choosing a cloud server for a short-term marketing campaign or promotion, price is often the first impression. however, judging whether a service is available needs to be based on technical capabilities, sla and emergency procedures, rather than a single price tag. this article provides practical reference around the key points of assessment to help you quickly determine whether it meets your protection needs for short-term activities.
understand the meaning of "us high-defense cloud server 20 yuan"
when you see the "20 yuan" mark, first confirm what kind of billing the number represents: whether it is a first-month promotion, hourly billing, daily billing, or only basic instance charges. don’t judge protection capabilities solely by price, but verify the specific descriptions of ddos protection levels, bandwidth caps, and regional nodes in the service description.
key indicators for evaluating ddos protection capabilities
focus on the types of attacks that can be mitigated (syn/udp/http flood, etc.), the maximum cleaning capabilities (bandwidth and concurrent connections), and whether layer 7/layer 3 protection is provided. if short-term activities involve high concurrency, give priority to solutions that have clear cleaning capabilities and can handle sudden traffic peaks.
network bandwidth and elastic scaling capabilities
evaluate the bandwidth upper limit and peak elasticity mechanism: short-term activity traffic is unpredictable, good services should support temporary expansion or elastic cleaning, and have clear billing policies. check whether there are multiple international exits, us regional acceleration nodes, and cdn or load balancing supporting services.
deployment speed and emergency response time
short-term activities are often sensitive to deployment and response times. confirm the supplier's online process, whether it supports immediate activation, and the sla for manual intervention and response after ddos alerts. the emergency response time is short and the one that supports work orders/telephone/instant channels is more reliable.
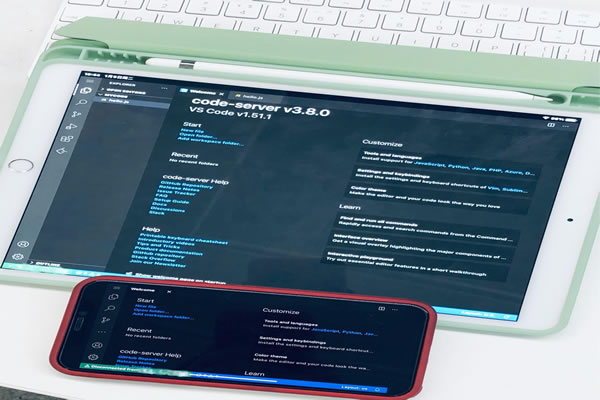
monitoring, logging and visualization capabilities
visual monitoring and detailed logs are crucial for quick troubleshooting during activity. check whether real-time traffic graphs, attack source analysis, traffic cleaning reports, and access log export functions are provided to quickly determine the attack situation and make adjustments.
contract terms, traffic billing and restrictions
carefully read the terms of service regarding bandwidth peaks, excess traffic billing, cleaning thresholds and traffic caps. if short-term activities exceed the basic quota, they may incur high fees or be speed-limited. clarifying the limit and billing model in advance can avoid unexpected costs.
testing and third-party verification recommendations
verify the protection effect through drill traffic tests or small-scale stress tests before going online, and require third-party testing or customer cases as reference. if possible, ask the vendor for past attack response cases or compliance certificates to demonstrate protection capabilities.
summary and suggestions
to determine whether the "u.s. high defense cloud server 20 yuan" meets short-term activity protection needs, it should be based on multi-dimensional evaluations such as ddos cleaning capabilities, bandwidth elasticity, deployment and response speed, monitoring and billing terms, etc. it is recommended to confirm specific technical indicators and sla first, verify through drills if necessary, and prepare backup plans to reduce activity risks.
- Latest articles
- Backup And Recovery Strategy To Develop A Zero-loss Disaster Recovery Plan For Thai E-commerce Vps
- Detailed Explanation Of The Impact Of Location Selection Of Hong Kong Station Cluster Computer Rooms On Network Quality And Delay
- Detailed Explanation Of The Impact Of Location Selection Of Hong Kong Station Cluster Computer Rooms On Network Quality And Delay
- Operational Suggestions: Management And Allocation Strategies Of Korean Station Group Native Ip In Multi-site Promotion
- German Server German Furry Social Media Communication Strategy And Seo Optimization Plan
- Case Study 2 Japanese Private Vps Love To Engage In Small Team Projects Practical Experience
- Compare The Reliability Differences In Obtaining Preferential Hong Kong Site Group Resources Through Different Channels
- Compare The Reliability Differences In Obtaining Preferential Hong Kong Site Group Resources Through Different Channels
- Backup And Disaster Recovery Solution For Database Migration To Alibaba Cloud's Singapore Server
- Advantages Of Hong Kong Cloud Server And Network Advantages Of Interconnection With Other Asia-pacific Nodes
- Popular tags
-
Analysis Of The Characteristics And Applicable Scenarios Of Dual-line Server Hosting In The United States
this article deeply explores the characteristics and applicable scenarios of dual-line server hosting in the united states, and provides professional selection suggestions for enterprises and individual users. -
Detailed Interpretation Of The Us High-defense Server Rental Process And Points To Note
this article explains in detail the rental process and precautions for high-defense servers in the united states, and provides you with professional guidance and suggestions. -
Successful Operation Experience Of Amazon Us Wechat Evaluation Group
this article shares the successful operation experience of amazon’s us site’s wechat review group to help sellers improve product reviews and sales.